TL;DR
“Keeping legacy applications alive “just to access old data” has become one of the most expensive and risky IT patterns in regulated industries. Decommissioning and application retirement are no longer a nice-to-have. They are increasingly forced by cybersecurity reality, regulatory pressure (including NIS2 and DORA), vendor end-of-life cycles, and the need to preserve evidence over long retention periods, especially in life sciences.
The winning strategy is not “turn everything off tomorrow.” It is: separate the data and evidence from the application, preserve it in an audit-ready way, and then decommission the system with confidence.“
The old logic: “We keep it running in case we need it”
Most organizations still have a portfolio of legacy systems kept alive for one reason: historical access.
- “We only use it twice a year.”
- “It’s read-only now.”
- “We can’t shut it down, compliance might ask for a record.”
- “We’ll migrate it later.”
This logic made sense when security threats were smaller, regulatory expectations were lighter, and infrastructure costs were acceptable.
That era is over.
Why decommissioning is now a must (not a choice)
1. Cybersecurity: legacy apps are the soft underbelly of your estate
Legacy systems typically sit outside modern security discipline:
- weak or partial MFA/SSO support
- outdated libraries and operating systems
- limited monitoring and alerting
- fragile patching and upgrade paths
- unclear ownership (“who still knows this system?”)
Even if the data is “old,” the system is a living attack surface. Attackers do not care that your ERP instance is from 2012. They care that it is reachable, vulnerable, and full of sensitive information.
Keeping legacy apps online increases your attack surface permanently. Decommissioning is one of the few actions that truly reduces risk, instead of just managing it.
2) Regulation: security and operational resilience requirements keep rising
Across the EU, regulation pushes organizations to demonstrate:
- stronger security controls
- resilient operations
- better governance of third-party ICT risk
- faster vulnerability management and incident response
- Two major drivers in that direction are:
- NIS2 (cybersecurity risk management and reporting expectations)
- DORA (ICT risk management and operational resilience in financial services)
Even when a regulation doesn’t explicitly say “retire legacy systems,” it effectively forces it by making it harder to justify:
- unsupported platforms
- weak controls
- missing evidence of monitoring and patching
- third-party dependency risk
The more regulated your environment becomes, the more “keep it alive” turns into “keep it compliant,” and that is where the costs explode.
3) Cost: the “read-only tax” is real and it compounds
Legacy systems cost money even when no one uses them:
- infrastructure (servers, storage, licenses)
- vendor support contracts
- security tooling and monitoring
- backups and DR
- specialist time (scarce knowledge)
- audit preparation and evidence retrieval
The hidden cost is the operational drag: teams become afraid to touch the system, changes take weeks, and every audit request becomes a mini project.
If you calculate total cost of ownership honestly, keeping legacy apps alive is often more expensive than retiring them properly.
4) Vendor end-of-life: you will be forced into upgrades you don’t want
Eventually every platform hits a wall:
- end-of-support
- incompatible dependencies
- security fixes no longer available
- database versions no longer supported
- hardware refresh cycles
At that point you are forced into one of two bad choices:
- do a full upgrade of a system you don’t want, just to keep historical access
- accept security and compliance risk
A controlled decommissioning strategy avoids both.
5) Life sciences and long-term evidence: retention is getting heavier, not lighter
In pharmaceutical and life sciences, there is a clear trend:
- stronger expectations around long-term preservation of analytical data, quality records, and evidence
- more scrutiny on data integrity principles (ALCOA+)
- greater emphasis on auditability, traceability, and inspection readiness
This creates a perfect storm:
- you must keep data longer
- you must keep it more verifiable
- and you must be able to retrieve it quickly during inspections
Keeping a legacy application alive is a fragile way to meet long-term preservation obligations. A better approach is to preserve the data and evidence independently, with integrity controls and exports that can stand up over time.
The core idea: retire the application, not the evidence
Decommissioning becomes feasible when you stop thinking of “the application” as the only way to preserve trust.
A modern application retirement approach typically means:
- Extract the required data, metadata, and context from the source system
- Preserve it in an immutable, audit-ready archive
- Ensure traceability (what came from where, when, under which rules)
- Provide search and retrieval without needing the legacy app
- Define exit packages (portability) so you are never trapped again
- Decommission the old system confidently
This is not just “storage.” It is controlled preservation of records and evidence.
What “good” looks like in practice (a quick checklist)
If you want to decommission responsibly, you should be able to answer “yes” to these:
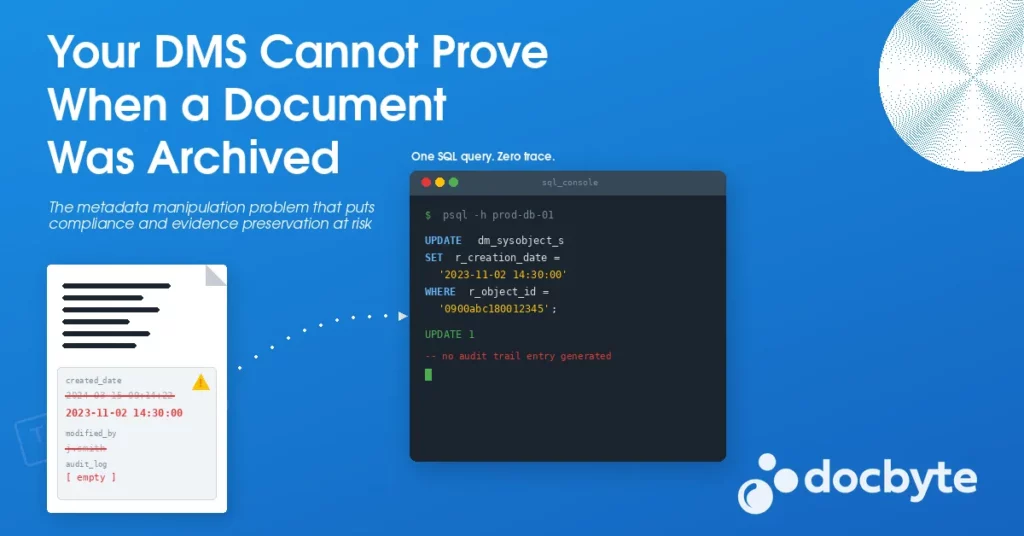
- Can we retrieve historical records without launching the legacy application?
- Can we produce an audit trail of who accessed what and when?
- Can we prove integrity independently (checksums, fixity, integrity reports)?
- Do we preserve the full context needed for interpretation?
- Do we have a defensible retention and disposition process?
- Can we export everything (data + metadata + evidence) if needed?
If not, decommissioning feels risky. If yes, keeping the old application becomes irrational.
The message for leadership: decommissioning is risk reduction, not just cost cutting
Organizations often frame decommissioning as a cost optimization project. That is too small.
Decommissioning is:
- cybersecurity risk reduction
- compliance risk reduction
- operational resilience improvement
- simplification of your estate
- protection of evidence and trust
In today’s environment, it is not an option to keep growing your legacy footprint.
Conclusion
Decommissioning is a must because the world around your systems changed:
- attackers got better
- regulators got stricter
- vendors retired old stacks
- retention periods got longer
- audits got tougher
The right response is not to keep legacy applications on life support. It is to build an approach where data and evidence remain accessible, verifiable, and audit-ready after the application is gone.